All industries must have a set of standards and procedures that allow them to operate safely and efficiently. This is why the electric utility industry looks to the North American Electric Reliability Corporation (NERC). The NERC provides standards that help electric and utility companies safeguard their technology and cyber assets from both physical and digital threats. These Critical Infrastructure Protection (CIP) guidelines also cover personnel and training guidelines to assist companies in hiring safe, accountable employees. Understanding NERC CIP is an essential part of maintaining an effective, reliable power grid. Make sure your company stays compliant with this overview of NERC CIP standards.
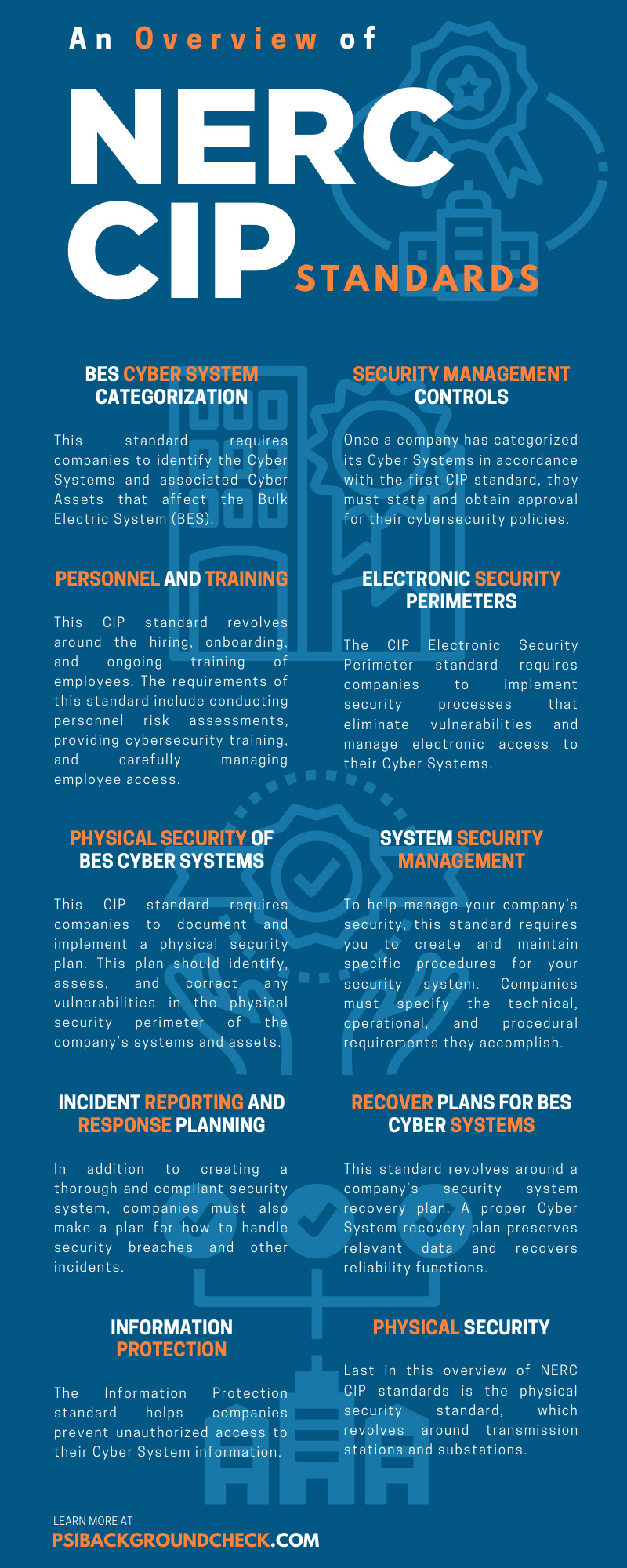
BES Cyber System Categorization
This standard requires companies to identify the Cyber Systems and associated Cyber Assets that affect the Bulk Electric System (BES). Companies must then categorize these systems by how much of an impact they could have on the BES if they were to be mishandled, lost, or compromised. By accurately identifying and categorizing these Cyber Systems, companies prioritize their most vulnerable systems and assets. This allows companies to better protect themselves against threats that could lead to mishandling, instability, and other negative effects on the BES.
Security Management Controls
Once a company has categorized its Cyber Systems in accordance with the first CIP standard, they must state and obtain approval for their cybersecurity policies. This standard ensures that companies document consistent, sustainable security management controls. By doing so, companies create a sense of accountability in protecting their Cyber Systems and, in turn, the Bulk Electric System. Every 15 months, companies must obtain approval of these security policies from a CIP Senior Manager. By following this standard, companies ensure they have the specific protections they need to handle any threats to their systems and assets.
Personnel and Training
This CIP standard revolves around the hiring, onboarding, and ongoing training of employees. The requirements of this standard include conducting personnel risk assessments, providing cybersecurity training, and carefully managing employee access. These requirements help companies prevent damage to or misuse of the BES at the hands of unauthorized or poorly trained employees. Companies should apply NERC CIP background checks and other aspects of this risk assessment to all personnel, including contractors, who have cyber or physical access to the company’s systems and assets.
Electronic Security Perimeters
Your company’s electronic security perimeter holds all your cybersecurity systems and assets. As such, protecting this perimeter should be a priority. The CIP Electronic Security Perimeter standard requires companies to implement security processes that eliminate vulnerabilities and manage electronic access to their Cyber Systems. Such processes can include anti-malware updates, patch updates, encryptions, multi-factor authentication systems, and extensible authentication protocol. In addition to these processes, companies should regularly perform a cyber vulnerability assessment of their Electronic Security Perimeters and any relevant access points.
Physical Security of BES Cyber Systems
In addition to maintaining electronic access and security, electric and utility companies must also create and manage a physical security perimeter of their Cyber Systems. This CIP standard requires companies to document and implement a physical security plan. This plan should identify, assess, and correct any vulnerabilities in the physical security perimeter of the company’s systems and assets. Additionally, companies should create physical access controls that aid in managing and protecting their Cyber Systems. Physical security plans should address these physical access controls, as well as physical monitoring, access logging, and maintenance of the security program.
System Security Management
To help manage your company’s security, this standard requires you to create and maintain specific procedures for your security system. Companies must specify the technical, operational, and procedural requirements they accomplish. In addition to listing these accomplishments, companies must also document test procedures, ports and services, patch management, and the prevention of potentially damaging software. Documenting these procedures helps hold companies accountable to their security systems, ensuring they are protecting their Cyber Systems and the overall Bulk Electric System.
Incident Reporting and Response Planning
In addition to creating a thorough and compliant security system, companies must also make a plan for how to handle security breaches and other incidents. This CIP standard puts forth specific incident response requirements, including how to identify and classify Cyber Security Incidents, reporting procedures, and proper handling procedures. This standard also details the roles and responsibilities of Cyber Security Incident response groups and personnel. These details and requirements help companies establish how to handle security breaches quickly and effectively.
Recover Plans for BES Cyber Systems
This standard revolves around a company’s security system recovery plan. A proper Cyber System recovery plan preserves relevant data and recovers reliability functions. CIP guidelines put forth recovery requirements that ensure companies can protect their Cyber Systems in the event of a security breach or other incident. These requirements can include a change of control, backing up media, and establishing backup and restoration processes.
Configuration Change Management and Vulnerability Assessments
This CIP standard serves to prevent and detect unauthorized changes to a company’s Cyber Systems and Cyber Assets. Unplanned or unauthorized changes can put your company’s systems and processes at risk, which can then threaten the entire Bulk Electric System. To make sure no unwanted changes occur, this standard requires companies to implement a baseline configuration for their operating systems or firmware. The company must then authorize and document any changes that occur outside this baseline configuration.
Information Protection
The Information Protection standard helps companies prevent unauthorized access to their Cyber System information. This standard specifies information protection requirements that all companies must follow, including storing, transferring, using, and disposing of Cyber System information. These requirements prevent leaks and unauthorized retrieval of information. Unauthorized access to this information can lead to compromised or unstable systems, putting your company and the entire BES at risk.
Physical Security
Last in this overview of NERC CIP standards is the physical security standard, which revolves around transmission stations and substations. This standard requires companies to identify and protect these stations and any associated control centers. Any physical damage or attacks to these facilities can render them inoperable, which can cause cybersecurity systems to become unstable or vulnerable.